Bitrefill Hack Exposes Lazarus Group in Sophisticated Cyberattack: Crypto Security Alert
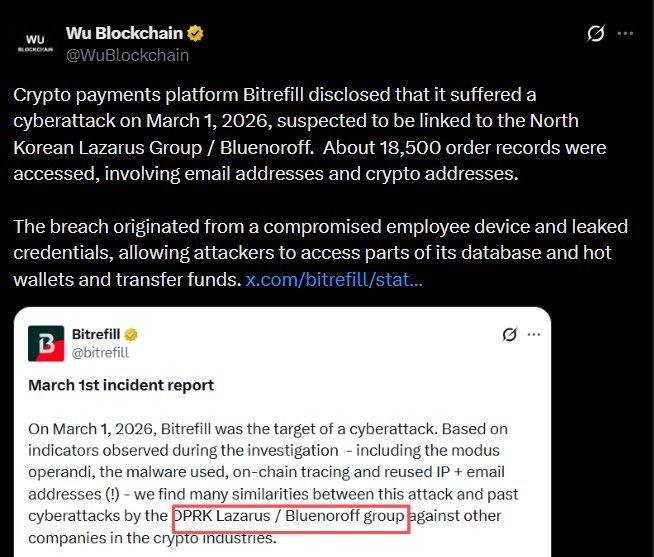
A major security warning has been issued across the cryptocurrency sector following Bitrefill's confirmation that its platform was compromised in a sophisticated cyberattack attributed to the Lazarus Group. The breach, which occurred on March 1 but was only disclosed on March 17, has triggered fresh concerns about systemic vulnerabilities and could precipitate a 10% correction in related security-focused tokens as investors reassess risk. While no specific financial losses have been quantified, the incident highlights the escalating threat from state-sponsored actors targeting crypto infrastructure.
Source: X Official
Focus remains on forensic analysis and attribution
Early findings suggest a highly organized cyber operation
The company emphasized transparency while continuing its internal review to understand the full scope of the breach.
What Bitrefill Does in the Crypto Ecosystem
Bitrefill is a platform that allows users to spend cryptocurrency on real-world services like gift cards, mobile top-ups, and travel bookings. It acts as a bridge between digital assets and everyday payments.
Enables indirect crypto spending globally
Serves users without requiring traditional banking systems
Attack Patterns Point Toward Lazarus Group
Investigators believe the Bitrefill Hack shares similarities with past cyberattacks linked to the Lazarus Group, also known as Bluenoroff.
Use of custom malware seen in earlier incidents
Familiar attack flow: phishing, then access, then lateral movement, then extraction
Reuse of infrastructure, such as IP addresses and email patterns
On-chain tracing also revealed suspicious fund movement patterns, including chain-hopping techniques often associated with Lazarus-linked laundering activity. This group is widely known as a state-backed collective responsible for some of the largest crypto-related breaches globally.
How the Breach Happened and What Was Affected
The attack began with a compromised employee's laptop, where attackers extracted a legacy credential. This allowed access to a snapshot containing sensitive production secrets. From there, access expanded into broader infrastructure, including parts of databases and certain crypto wallets.
Suspicious purchasing activity first alerted the team
Gift card inventory and supply systems were exploited
Hot wallets were reportedly drained, with funds moved to attacker-controlled addresses. Systems were immediately taken offline to contain the damage. According to internal findings, the main target was financial assets rather than user data.
Around 18,500 purchase records were accessed, including limited details such as email addresses, crypto wallet information, and IP metadata. For roughly 1,000 transactions, encrypted names may also have been exposed due to possible access to encryption keys. Affected individuals have already been notified.
The company clarified that it stores minimal personal data and relies on external providers for KYC verification, reducing the overall exposure risk.
Response Measures and What This Means for Crypto Security
Following the Bitrefill Hack, the firm has taken steps to strengthen its cybersecurity framework and prevent future incidents.
Conducting external audits and penetration testing
Improving access controls, monitoring systems, and response protocols
Users have been advised to remain cautious of suspicious communications, though no immediate action is required at this stage.
Conclusion:
This incident highlights a broader issue in the digital asset space: as adoption grows, platforms handling crypto payments become prime targets for advanced threat actors. Strengthening infrastructure, improving monitoring, and ensuring rapid response mechanisms will be critical for long-term trust. The Bitrefill Hack serves as a reminder that even established platforms must continuously evolve their security posture to stay ahead of increasingly sophisticated cyber threats.

