Google Exposes Coruna: The iPhone Exploit Kit Draining Crypto Wallets
Your iPhone's security just got a lot more interesting—and not in a good way. Google's Threat Analysis Group has pulled back the curtain on 'Coruna,' a sophisticated exploit kit designed specifically to target iOS devices and siphon digital assets from crypto wallets.
The Stealthy Infiltration
Coruna doesn't knock on the front door. It bypasses Apple's vaunted security through a chain of zero-day exploits, slipping past defenses to install persistent malware. Once inside, it lies dormant, waiting for you to open your cryptocurrency wallet app. That's when it strikes, intercepting transactions and redirecting funds to attacker-controlled addresses. It's a digital pickpocket operating at the silicon level.
Why Your Wallet is the Target
The logic is brutally simple for threat actors: follow the money. As cryptocurrency adoption grows, so does the value stored on mobile devices. Coruna represents a professionalization of crypto-focused cybercrime—moving from scatter-shot phishing attempts to surgical, high-value exploits. It turns the device in your pocket into a liability. The old adage 'not your keys, not your crypto' gets a sinister twist: even your keys aren't safe if your device is compromised.
The Industry's Cold Shower
This isn't just another malware alert. Coruna is a wake-up call for the entire crypto ecosystem, highlighting a critical vulnerability that sits between cold storage paranoia and hot wallet convenience. It exposes the uncomfortable truth that user-friendly mobile access creates a lucrative attack surface. Security researchers are now racing to dissect the full kill chain, while wallet developers are forced to re-evaluate their in-app security assumptions. Meanwhile, exchange compliance teams are probably drafting new warnings about device hygiene—as if anyone reads those.
In the high-stakes game of digital finance, your phone is now the ultimate perimeter. And as one cynical trader might note, this exploit kit probably has a better risk-adjusted return than most altcoins this quarter.
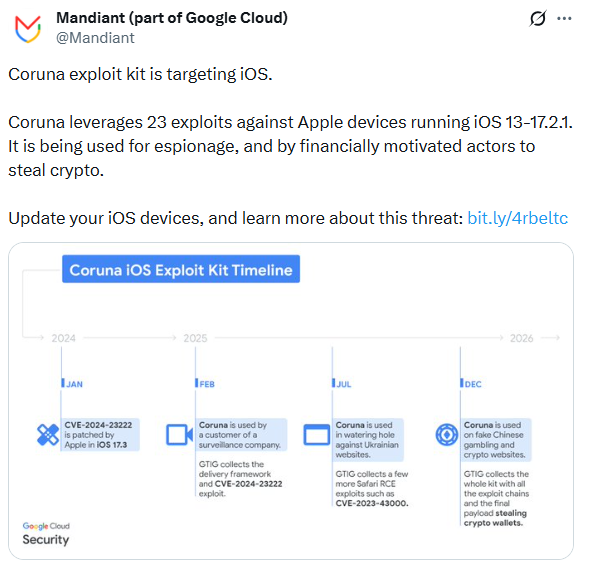
The Coruna iPhone exploit kit is highly advanced, containing 23 different hacking methods organized into five full "exploit chains". Some of these techniques were previously unknown to the public. What makes this situation scary is how the tool has moved between different groups. It was first used by a surveillance company, then by a Russian spying group, and finally by a criminal gang in China focused on stealing money. This shows a growing market where high-level spy tools are being sold to common hackers.
How the Coruna iPhone exploit kit Hacks Your Private Data
The main goal of this attack is to steal cryptocurrency. Hackers use fake websites, such as a cloned version of the WEEX crypto exchange, to lure victims. If you visit one of these sites on an older iPhone, a hidden script runs in the background without you knowing.
How the Theft Happens
The kit first checks your iPhone model and software version to see if it can be hacked.
It uses flaws in the Safari browser to gain "root" access to your entire phone.
A program called "PlasmaLoader" scans your device for sensitive words like "backup phrase" or "bank account".
It targets popular apps like MetaMask, Exodus, Coinbase Wallet, and Bitget to steal seed phrases and private keys.
Once it finds your data, it sends it to an external server controlled by the hackers.
The Debate Over Its Origins
Researchers are still arguing about where this kit came from. The security firm iVerify claims the code looks very similar to tools built by the U.S. government that may have "spun out of control". However, other experts from Kaspersky say there is no solid proof yet that the code was copied from known government frameworks. Regardless of its origin, the toolkit cost millions of dollars to develop and is now being used to attack regular users.
Future Outlook: Expert Analysis
The discovery of the Coruna toolkit is a wake-up call for the mobile industry. We are seeing a "second-hand" market for cyber weapons where state-level tools are being recycled for financial crime. This means that targeted spyware is now being used for mass attacks against anyone holding crypto. In the future, we expect hackers to become even better at hiding their scripts inside everyday websites.
The best way to stay safe is simple: keep your iPhone updated. Google and Apple both confirm that the Coruna iPhone exploit kit does not work on the latest versions of iOS, such as iOS 17.3 and newer. If your phone is too old to update, you should turn on "Lockdown Mode" in your settings. The hackers designed this kit to automatically stop if it detects Lockdown Mode, as it makes the device too hard to crack.
Cryptocurrency and mobile security involve high risks. This article provides information based on current security reports and does not guarantee total protection. Always consult official Apple security guides for the best advice on your specific device.

