Forged Messages Drain $3M from CrossCurve Protocol: Crypto’s Latest Smart Contract Exploit
Another day, another multi-million dollar heist—this time, forged messages bypassed CrossCurve's defenses, siphoning funds in a flash.
The Attack Vector: Signature Spoofing
The exploit didn't brute-force the protocol; it tricked it. Attackers crafted fraudulent authorization messages, convincing the system to release funds without proper checks. It's a classic case of digital forgery meeting decentralized finance—where a single spoofed signature can unlock a vault.
Where the Security Broke Down
CrossCurve's verification logic had a gap. The protocol validated the *existence* of a message but not its *authenticity* in certain edge cases. That loophole let attackers mimic legitimate transactions, moving $3 million worth of assets before alarms sounded. No private keys were stolen—just trust in the code, exploited.
The Aftermath and the Industry's Persistent Blind Spot
Funds moved to mixers, traces faded, and the protocol scrambled to patch the hole. It's the same cycle: build, hack, respond. Meanwhile, traditional finance regulators smirk—another 'unbreakable' system learning a $3 million lesson in humility. Audits? Passed. Stress tests? Completed. Yet the ingenuity of attackers always seems to outpace the diligence of defenders.
Smart contracts remain both crypto's greatest innovation and its most glaring liability. Until the industry treats security as a core feature—not an afterthought—these headlines will keep coming. The code is law, until someone rewrites it mid-execution.
What Happened? CrossCurve Crypto Hack News
CrossCurve, previously EYWA, has verified that its cross-chain liquidity protocol was hacked because of a severe smart contract vulnerability. This event caused it to lose around $3 million of its PortalV2 contract on several blockchain networks.
According to the team, the attack was caused by a lack of gateway validation that enabled the attackers to forge cross-chain messages and bypass validation to unlock tokens without authorization.
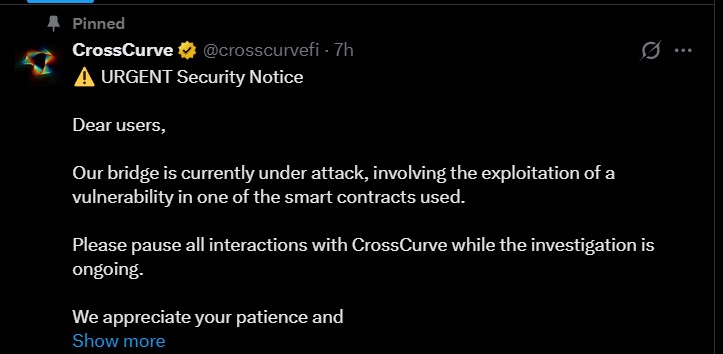
Source: Official X
How Did the Attack Work? Understanding the Vulnerability
Security analysis showed that the vulnerability was in the ReceiverAxelar contract. Precisely, its expressExecute option might be called directly using spoofed messages, which allowed the attackers to circumvent the built-in gateway verification tests.
This exploit is similar to other high-profile bridge attacks of the past, including the Nomad hack of 2022, indicating that protocols are still vulnerable to attacks, according to blockchain security firm Defimon Alerts.
CrossCurve’s Response: Bounty and Legal Action
CrossCurve began taking action to avert harm and contact affected users:
The money was sent to 10 addresses. Non-malicious holders have an opportunity to keep 10% in the form of a bounty.
The rest of the money has to be refunded to an address beginning with 0x624E.
The addresses will be considered malicious in case of non-refundment of funds or failure on the part of holders to communicate with CrossCurve within 72 hours.

Source: X
The protocol has threatened that non-compliance will be followed up by judicial proceedings, which include:
Criminal reporting and civil litigation.
Collaboration with exchanges and Circle to freeze assets.
Malicious addresses and the results of the analysis should be disclosed publicly.
Who’s Behind CrossCurve? Background of the Protocol
CrossCurve is a cross-chain DEX and cross-chain consensus bridge that runs transactions with a variety of validation protocols, such as Axelar, LayerZero, and EYWA Oracle Network,k in collaboration with Curve Finance.
The project also focused on its security-first design and stated that the likelihood of multiple cross-chain protocols being compromised at the same time is almost zero. Remarkably, Michael Egorov, the founder of Curve Finance, invested in CrossCurve in September 2023, and the protocol raised $7 million with the help of venture capitalists.
What This Means for Users: Should You Be Concerned?
Curve Finance recommended that userwhoat have invested in Eywa-related pools should check their holdings and think about withdrawing their votes. CrossCurve also advised everyone to cease communications until the investigation is over.
Security experts caution that bridge protocols are a risky field in DeFi, particularly when the project relies on multi-chain validation systems.
Conclusion
The CrossCurve crypto hack news highlights the persistence of cross-chain bridge vulnerabilities, impacting millions of users, and the necessity to be cautious about smart contract security and user behavior on DeFi platforms.
Disclaimer: This is not financial advice. Please DYOR before investing. CoinGabbar is not responsible for any financial losses. Crypto assets are highly volatile, and you can lose your entire investment.

