BREAKING: Solana Memo Feature Exploited in Stealth Malware Attack Targeting Crypto Wallets
Security researchers have issued an urgent warning after discovering a novel malware campaign exploiting Solana's public memo field to secretly steal cryptocurrency wallet data and hardware wallet recovery phrases. The attack transforms a standard blockchain feature into a covert command-and-control channel, allowing attackers to update malicious instructions without altering the malware itself. This campaign represents a new evolution of the GlassWorm malware, active since 2022, and highlights the inherent risks of immutable, decentralized data structures being weaponized against users.
Solana memos act as a dead drop resolver
According to security researchers from Aikido, the attack has three stages or three payloads. The first stage/payload is just an entry point. It begins when a developer installs a malicious package from open source repositories like npm, PyPI, GitHub, or the Open VSX marketplaces.
The malware then checks if the system locale is Russian and if so, it does not proceed with the attack. This is because the attackers are likely based in Russia and do not want to get caught by authorities. Once installed, the malware uses the Solana blockchain to fetch the attacker’s command-and-control (C2) server IP address. It looks for a specific transaction on Solana that contains the C2 server’s IP address in the memo field.
The malware then connects to the C2 server and starts the second stage of the attack. In this stage, the malware looks for crypto data like seed phrases, private keys, and even screenshots of wallets. It targets browser extension wallets like MetaMask, Phantom, Coinbase, Exodus, Binance, Ronin, Keplr, and more.
The malware also looks for browser data like login sessions, session tokens, and cloud access. This means it can access centralized exchange accounts, npm, GitHub, and AWS accounts.
After collecting the data, the malware compresses it into a ZIP file, and sends it to the attacker’s server.
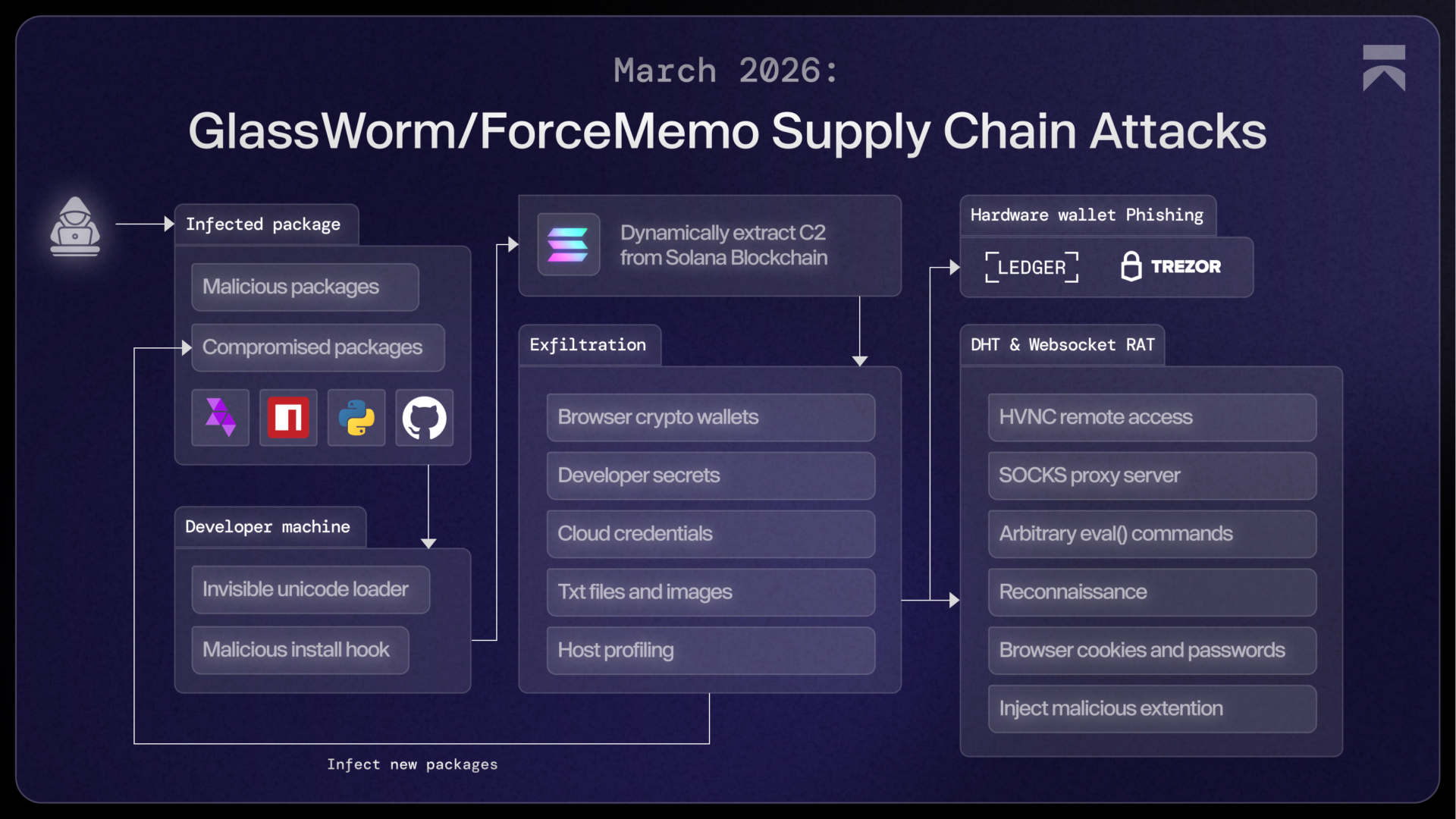
Hardware wallets targeted via phishing
The last payload splits into two parts. The first part is a .NET binary that looks for hardware wallets like Ledger and Trezor. If it finds one, it shows a fake error message that tricks the user into entering their recovery phrase.
The second part is a WebSocket-based JavaScript RAT (remote access trojan) that steals browser data. It also installs a fake Chrome extension that monitors specific sites like exchanges and steals cookies in real time. It’s downloaded through a Google Calendar event as a dead drop resolver. This approach allows the attacker to hide the real server, bypass security filters and it acts as an indirect delivery layer.
Unlike the second stage, where the malware only steals browser data, this RAT has live control. It stays active and monitors the browser. It captures new cookies, tracks active sessions like logged-in exchange accounts, logs keystrokes, and takes screenshots. Moreover, it allows the attacker to run commands on the victim’s machine.
Its difficult to remove GlassWorm. The malware can re-download itself and it can survive reboots. It also uses fallback methods like DHT (Distributed Hash Table) lookups and Solana memos to find the control server.
Since there’s no central server, and the data is shared across many computers, it becomes difficult for defenders to block the attack at the network level.
This attack is very dangerous. It highly severe because it combines crypto theft, full system control, and unremovable network.Don’t just read crypto news. Understand it. Subscribe to our newsletter. It's free.

