North Korea’s Lazarus Group Likely Behind Kelp DAO’s $292M Exploit, LayerZero Reveals
LayerZero has identified North Korea's Lazarus Group as the likely perpetrator behind the $292 million Kelp DAO exploit, warning that a single-point-of-failure in the protocol's verifier setup enabled the largest DeFi hack of 2026. The breach triggered a 7% sector-wide correction, wiping $6.3 billion from total value locked as DeFi plunged to $85 billion within 24 hours, according to DefiLlama data.
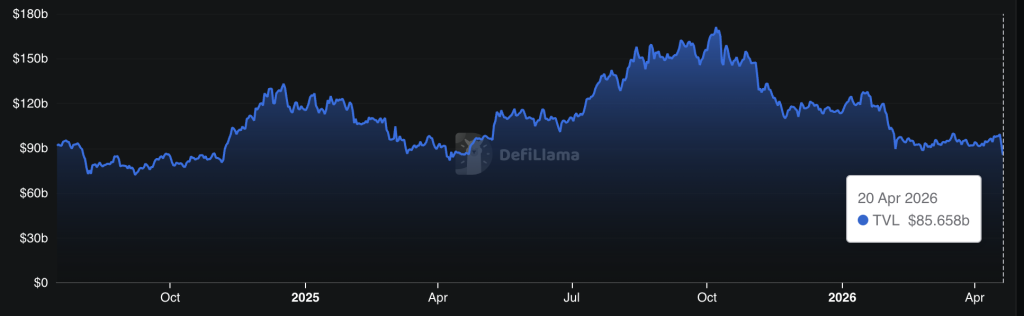 DeFi Total Value Locked / Source: DefiLlama
DeFi Total Value Locked / Source: DefiLlama
The attribution lands not as a closed finding but as a probabilistic claim: LayerZero says Lazarus is the likely perpetrator, not a confirmed one. What that distinction means for the protocol, its users, and the cross-chain security model is the question this story answers.
Key Takeaways:- Attribution source: LayerZero conducted the post-incident investigation and named North Korea’s Lazarus Group – specifically the TraderTraitor subgroup – as the likely perpetrator.
- Technical root cause: Kelp DAO operated a 1-of-1 DVN (single decentralized verifier node) setup, ignoring LayerZero’s repeated recommendations for multi-verifier redundancy.
- Exploit amount: Approximately $292 million drained from Kelp DAO’s rsETH pool; no LayerZero protocol code or private keys were compromised.
- Market impact: DeFi TVL fell 7% in 24 hours to $86 billion following the incident.
- Response: LayerZero decommissioned affected RPC nodes and restored full DVN operations; law enforcement collaboration is ongoing for fund tracing.
- Watch: Whether Kelp DAO announces a compensation mechanism and whether additional cross-chain protocols operating single-DVN configurations move to remediate before the next attack.
LayerZero’s Kelp DAO Lazarus Findings: What a Single-Point Failure Actually Means in Cross-Chain Architecture
The exploit’s mechanism was multi-step and precise. Attackers poisoned the RPC infrastructure feeding LayerZero’s decentralized verifier network, then launched a DDoS attack designed to force failover to compromised backup nodes.
With the verifier network redirected, the system validated fictitious cross-chain transactions, and $292 million in rsETH exited Kelp DAO’s pool before the fraud was detected.
Earlier today we identified suspicious cross-chain activity involving rsETH. We have paused rsETH contracts across mainnet and several L2s while we investigate.
We are working with @LayerZero_Core, @unichain, our auditors and top security experts on RCA.
We will keep you…
The critical enabler: Kelp DAO ran a 1-of-1 DVN configuration, meaning a single verifier node stood between the protocol and catastrophic failure. LayerZero had flagged this architecture as inadequate – multiple times, according to the investigation – and recommended a multi-DVN setup consistent with industry best practices for redundancy. Kelp DAO did not act on those recommendations.
A multi-DVN setup would have required attackers to compromise several independent verification nodes simultaneously, a substantially harder technical lift. The 1-of-1 setup collapsed that barrier entirely. As Ripple CTO David Schwartz put it on X: “The attack was way more sophisticated than I expected and aimed at LayerZero infrastructure taking advantage of KelpDAO laziness.”
LayerZero’s response was surgical: the team decommissioned all affected RPC nodes post-incident and fully restored DVN operations without broader contagion to other protocols using the same infrastructure. No LayerZero protocol code was compromised. No private keys were exposed. The failure was architectural, not foundational – a distinction that matters enormously for the protocol’s credibility but does nothing to recover the $292 million.
Why North Korea Attribution Changes the Threat Model for All of DeFi
LayerZero’s Lazarus Kelp DAO attribution, framed as likely, not confirmed, is consistent with an established and accelerating pattern.
The TraderTraitor subgroup, a known Lazarus operational unit, was preliminarily identified in the forensic analysis. LayerZero is actively collaborating with global law enforcement on fund tracing, suggesting the attribution carries enough evidentiary weight to involve state-level investigative resources.
lazarus stole $7B+ since the beginning of crypto
7 fucking billion
how do you even cash that out?
Lazarus has been tied to some of the largest crypto thefts on record, including the $625 million Ronin Network hack in 2022 and a string of DeFi protocol exploits that have collectively funneled billions into DPRK’s weapons programs, according to U.S. Treasury and UN assessments.
North Korea’s crypto operations extend well beyond direct exploits – the regime has also embedded operatives inside Web3 companies under fabricated identities, a parallel track that widens the attack surface beyond infrastructure alone.
Cross-chain protocols are structurally attractive targets for this class of actor. They sit at high-value junctions between multiple chains, often carrying pooled liquidity that dwarfs any single application’s balance, and their security depends on verifier networks that can become single points of failure when misconfigured. RPC poisoning as a tactic against verifier networks represents a novel escalation – one that security researchers say is now documented and replicable.


Log in to Reply
Log in to comment your thoughtsComments
Related Articles
|Square
Get the BTCC app to start your crypto journey
Get started today Scan to join our 100M+ users