Kraken Refuses Extortion Demand Over Stolen Crypto User Data - Takes Public Stand Against Criminal Group
Kraken's Chief Security Officer Nick Percoco issued a stark warning to the cryptocurrency industry on April 13, 2026, revealing the exchange is being extorted by criminals who obtained videos of internal systems containing customer data. In a bold institutional signal during a period of fragile exchange trust, Kraken publicly refused to pay the ransom and confirmed collaboration with federal law enforcement across multiple jurisdictions to pursue arrests. The breach, which affected approximately 2,000 individuals representing roughly 0.02% of users, resulted from insider recruitment rather than full system compromise, with customer funds remaining secure throughout the incident.
How Kraken Crypto Breach and Extortion Mechanics Actually Worked
This was not a credential-scraping exploit or a protocol vulnerability. The entry point in both the February 2025 incident and the current extortion threat was insider recruitment; compromised individuals within Kraken’s organization granted access to internal systems, enabling reconnaissance rather than a full breach.
The access appears to have been read-only, sufficient to capture customer data on video without triggering immediate detection.
Percoco confirmed that Kraken received a tip about a video showcasing sensitive customer information from its internal crypto systems, the same mechanism used in the February 2025 case, when a similar video surfaced on a criminal forum.
In both instances, an internal actor was identified. The criminals are now threatening to distribute those videos and associated customer data to local media and across social networks unless Kraken complies with unspecified demands. The precise dollar figure of the extortion demand has not been publicly disclosed.
Kraken Security Update
We are currently being extorted by a criminal group threatening to release videos of our internal systems with client data shown if we do not comply with their demands. It’s important to start with the most important points: our systems were never…
The pattern Percoco described is deliberate and scalable. “We have been collaborating with industry partners and law enforcement to investigate and disrupt insider recruitment efforts targeting not only crypto companies, but also gaming and telecommunications organizations,” he said.
That’s not opportunistic hacking. That’s a coordinated recruitment infrastructure operating across high-value data sectors, and Kraken is explicitly naming it as such, which matters for how the industry should respond.
Emerging crypto theft vectors increasingly target infrastructure access rather than on-chain exploits, and insider recruitment fits that same threat profile.
What User Data Was Actually Exposed – and What That Enables
Kraken crypto has not publicly specified which data categories were captured in the videos, including KYC documentation, wallet addresses, transaction history, or account metadata.
What is confirmed: approximately 2,000 individuals had their information viewed, and Kraken states it has already contacted everyone at risk. The access was read-only, and internal systems were not breached in the fuller sense of data being exfiltrated at scale.
The practical risk for affected users is not account takeover; no funds were accessed. The risk is targeted social engineering and physical exposure.
(Source – TRM Labs)
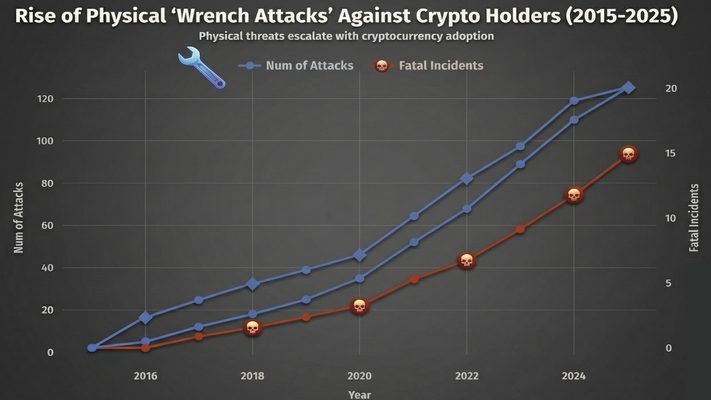
With names, addresses, and account-level data in criminal hands, affected users become targets for the same wrench attack vector that CertiK tracked, resulting in over $40 million in losses last year.
That figure is almost certainly undercounted, given the norms of underreporting. Kraken’s outreach to affected users is the right procedural step; whether that outreach included specific security guidance, hardware key recommendations, address changes, or heightened vigilance is not confirmed.


Log in to Reply
Log in to comment your thoughtsComments
Related Articles
|Square
Get the BTCC app to start your crypto journey
Get started today Scan to join our 100M+ users