URGENT WARNING: Bonk Fun Website Hijacked - Live Exploit Actively Draining User Funds
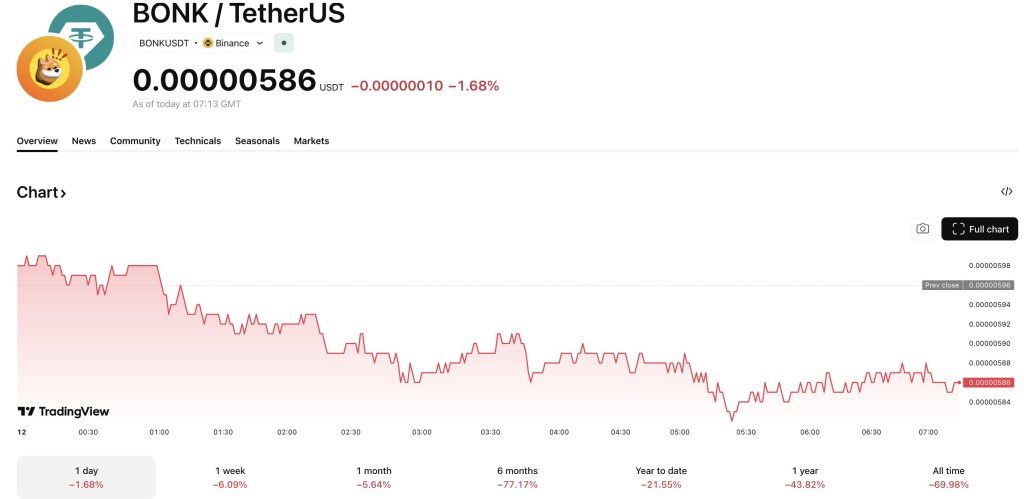
The official Bonk Fun website, a major Solana memecoin launchpad, has been seized by a malicious actor deploying a live wallet drainer, prompting an urgent 'DO NOT INTERACT' warning from the platform's team. The security breach coincides with a sharp 10% correction in the BONK token, compounding losses in a year where the memecoin has already plummeted 45%. Users connecting wallets to the compromised site face immediate asset theft as the exploit remains active.
 SOURCE: TradingView
SOURCE: TradingView
How Did the Malicious Actor Breach the Bonk Fun Front-End?
The attack vector exploits user trust rather than the blockchain infrastructure itself. According to X user SolportTom, the platform’s operator, hackers hijacked a team account to force a drainer onto the domain. This is not a smart contract failure; it is a front-end takeover.
Visitors to the site are currently greeted with a fake terms-of-service message. This pop-up, which mimics standard compliance requests, is the trigger mechanism.
To answer the concerns I’m seeing:
1. No if you connected to bonk fun in the past you’re not affected
2. No if you trade bonk fun tokens on terminals etc you’re not affected
3. The only people affected were people who signed a fake TOS message on the bonkfun domain after…
If you sign this request, the protocol grants the attacker permission to empty your wallet, and it will happen within seconds.
“A malicious actor has compromised the BONKfun domain,” the platform announced via its official X account. “Do not interact with the website until we have secured everything.”
How Much Has Been Drained and Who Is Affected
The Bonk.fun team hasn’t confirmed how much was lost to the hack, but has stated that losses are “minimal,” attributing the low damage to the developers’ rapid detection.
Only users who interacted with the fraudulent terms-of-service prompt during the active hijack window were affected. However, the exact dollar figure verified by on-chain analysis remains pending.
![]() AAVE ORACLE GLITCH TRIGGERS $26M IN WRONGFUL LIQUIDATIONS
AAVE ORACLE GLITCH TRIGGERS $26M IN WRONGFUL LIQUIDATIONS
A pricing oracle error on Aave caused about $26million in wstETH positions across 34 accounts to be unfairly liquidated after the system reported an incorrect exchange rate, with affected users set to be compensated. pic.twitter.com/qMbsAhQnnl
This incident mirrors broader risks in the sector, as an Aave oracle glitch triggered liquidations earlier this year due to interface and data anomalies.
While the mechanics differ, the result for user funds is identical: an unexpected loss due to a technical compromise.
Phishing attacks like this are becoming industrialized. According to Chainalysis, overall crypto scam losses reached approximately $17Bn in 2025.
The shift toward domain hijacking indicates attackers are bypassing protocol security to target the user interface directly.
What Bonk.fun Users Need to Do Right Now
If you have visited Bonk.fun in the last 24 hours, assume your session security was compromised. Front-end attacks often bypass standard defenses, as the recent discovery by Ledger researchers of an Android flaw enabling wallet seed phrase theft demonstrates.
Take these steps immediately:
- Disconnect your wallet: Remove Bonk.fun from your connected sites list in your wallet settings.
- Revoke approvals: Use a tool like Revoke.cash to revoke any recent permissions granted to Bonk.fun contracts.
- Check your history: Verify that no unauthorized transfers have occurred.
“We understand a lot of people are scared and rightly so, but we’re doing everything in our power to fix the situation,” SolportTom wrote.
Users should now sit tight and wait for an official “all-clear” from the Bonk.fun X account before returning to the site.
If the site remains compromised for another 24 hours, user migration to rival launchpads like Pump.fun will likely accelerate, and Bonk.fun may struggle to regain whatever was left of its userbase.
If the team resolves the DNS hijack quickly and refunds the “minimal” losses, confidence may stabilize, but the pressure is now on the operators to prove the domain is safe.

