Critical Android Chip Flaw Exposes Private Keys in Under 45 Seconds - Millions of Phones at Risk
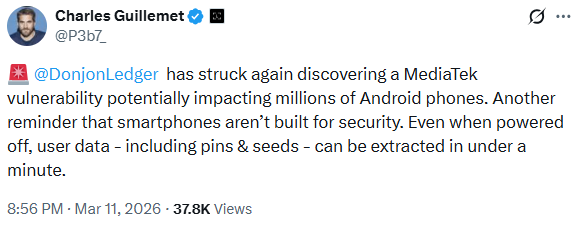
A critical security warning is being issued for millions of Android users worldwide. Security researchers from Ledger's Donjon team have uncovered a hardware-level flaw in MediaTek processors that allows hackers to extract private cryptographic keys in under 45 seconds, potentially exposing cryptocurrency wallets and sensitive financial data. The vulnerability resides in the secure boot chain of chips powering approximately 25% of global Android devices, creating what experts describe as a systemic threat to mobile-based digital asset security.
Researchers proved the danger by testing a Nothing CMF Phone 1, a modular device released in 2024. By simply connecting the phone to a laptop via USB, they bypassed the security systems in just 45 seconds. This high-speed attack worked even while the device was powered off. The team successfully recovered the device PIN, unlocked the storage, and stole "seed phrases" from top crypto wallets. These affected apps include Trust Wallet, Kraken Wallet, Phantom, and Rabby.
This discovery marks a big shift in the fight for mobile security. While the industry has long focused on remote hacks, this research shows how fast a physical attack can work on standard hardware. The ability to pull keys from a device while it is turned off skips almost every software protection we use. This includes screen locks and fingerprint scanners.
Technical Guide to the Android Chip Flaw and MediaTek Security
The reason this Android chip flaw is so dangerous is that it happens during the boot process. This is before the phone’s operating system even starts up. If a hacker gets physical access to your phone, they can use this window to pull out the root "keys" that protect your storage. Once they have these keys, they can read your data on a separate computer and quickly guess your PIN.
Who Is at Risk?
While the test focused on one 2024 model, the affected chips are very common. Many major brands use MediaTek hardware. You may be at risk if you use a phone from:
Samsung, Motorola, or Xiaomi
OPPO, Vivo, or POCO
Solana Seeker (the crypto-specific phone)
Beyond just crypto assets, this flaw could expose your private messages, photos, and login details stored on the hardware.
Industry Response and Responsible Disclosure
Ledger followed professional rules by notifying MediaTek and the security firm Trustonic 90 days before making the news public. MediaTek confirmed they sent a fix to phone makers on January 5, 2026. However, the rollout of these patches depends on each individual smartphone company. The vulnerability is now tracked under the name CVE-2025-20435.
Expert Analysis: The Future of Mobile Security
This Android chip flaw is a strong reminder that mobile phones were never built to be high-security vaults. Most phone chips are designed for speed and low cost, not for protecting private keys. We expect to see more people moving their money to dedicated "Cold Storage" hardware wallets. These devices use special "Secure Elements" to keep secrets away from the main system. For now, you should install any available security updates immediately to make sure your device is as safe as possible.
This article is for informational purposes and is not financial or security advice. Mobile security threats evolve rapidly; always prioritize using cold storage for significant digital asset holdings.

